
An elaborate scam is underway that pretends to be a free game giveaway site, but instead hacks a user's Steam account, takes control over it, and then incorporates the new victim into their attack by targeting other players.
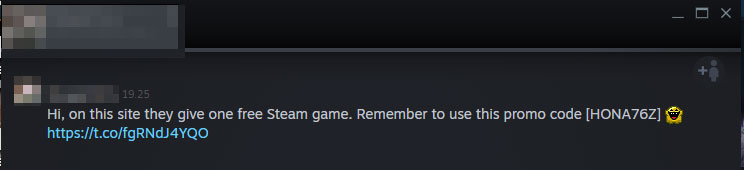
The scam works by attackers hacking into Steam accounts and sending messages to the victim's friends that they can get a free Steam game by going to a site and entering a promo code.
When a user clicks the URL they will be brought to the URL http://steamsafe.fun/?ref=freegame, which will then redirect a user to one of the attacker's currently working scam sites. These sites, shown below, pretend to be a giveaway site for free Steam games.
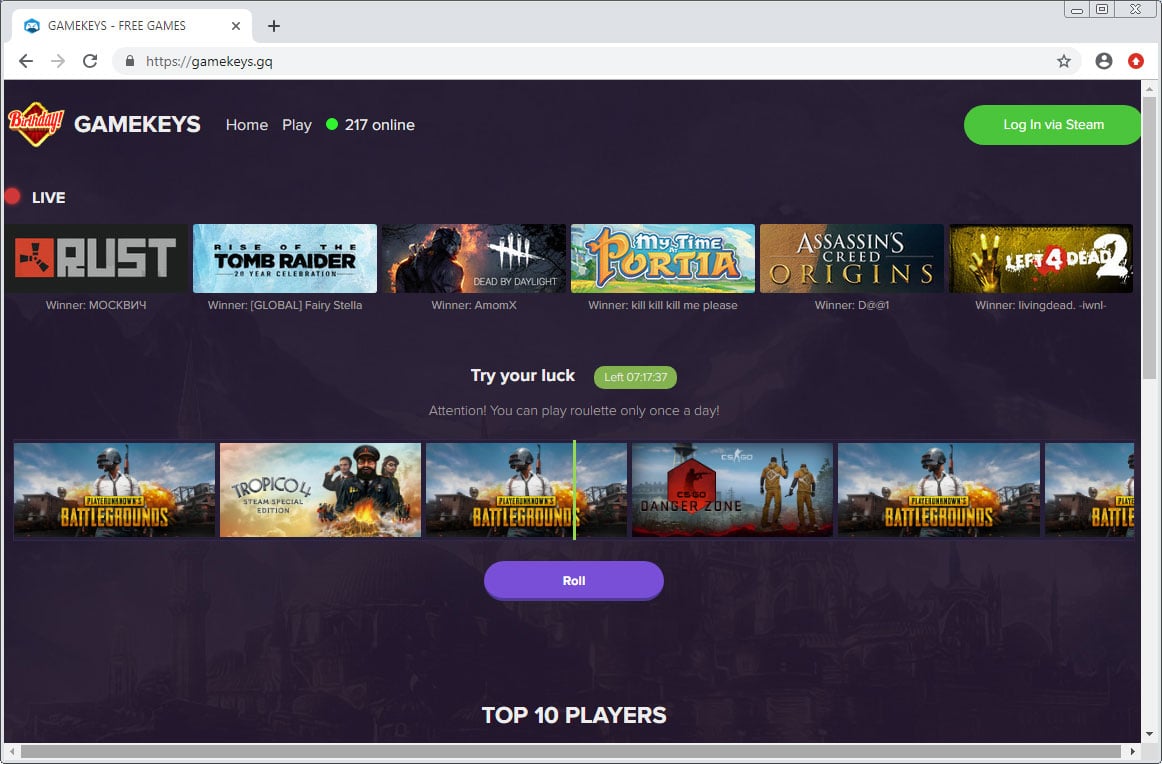
When a user clicks on the Roll button, the site will pretend to select a random game from a list of of popular ones such PUBG, CSGO, Tropico 4, ARK: Survival Evolved, Assassin's Creed, and more.
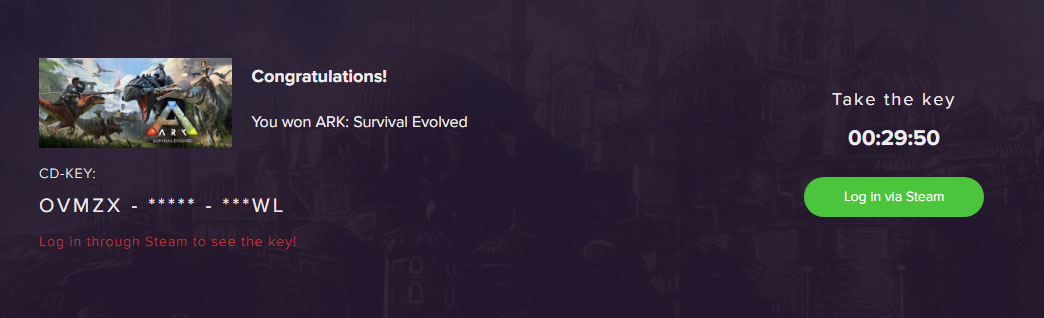
It will then display part of a Steam code and state that you need to login to Steam to claim the game.
When a user clicks on the login button, it will show a fake Steam single sign-on (SSO) login page that looks like it's from the Steam site, but is actually hosted on the scam site.
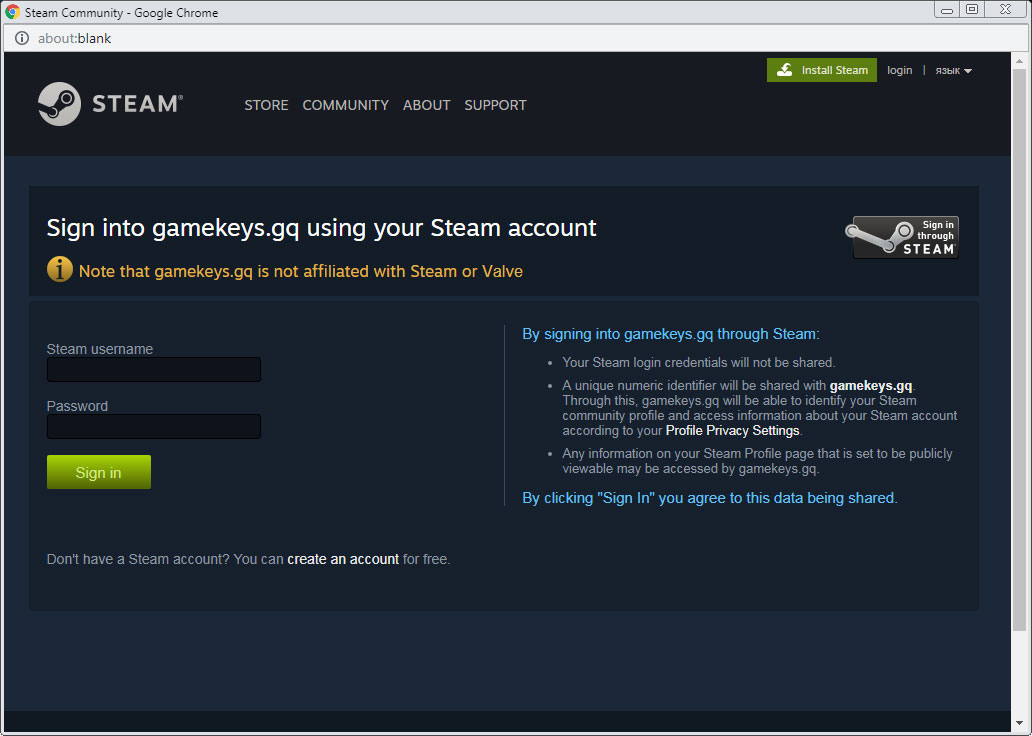
If you enter your credentials, the site will use them in the background to try and login to the user's Steam account. If Steam Guard requests a code, it will popup and ask the user for the code sent to their email address or provided by their 2FA app. This allows it to bypass 2-factor authentication that may be setup on the user's account as they are providing the attackers with the code.
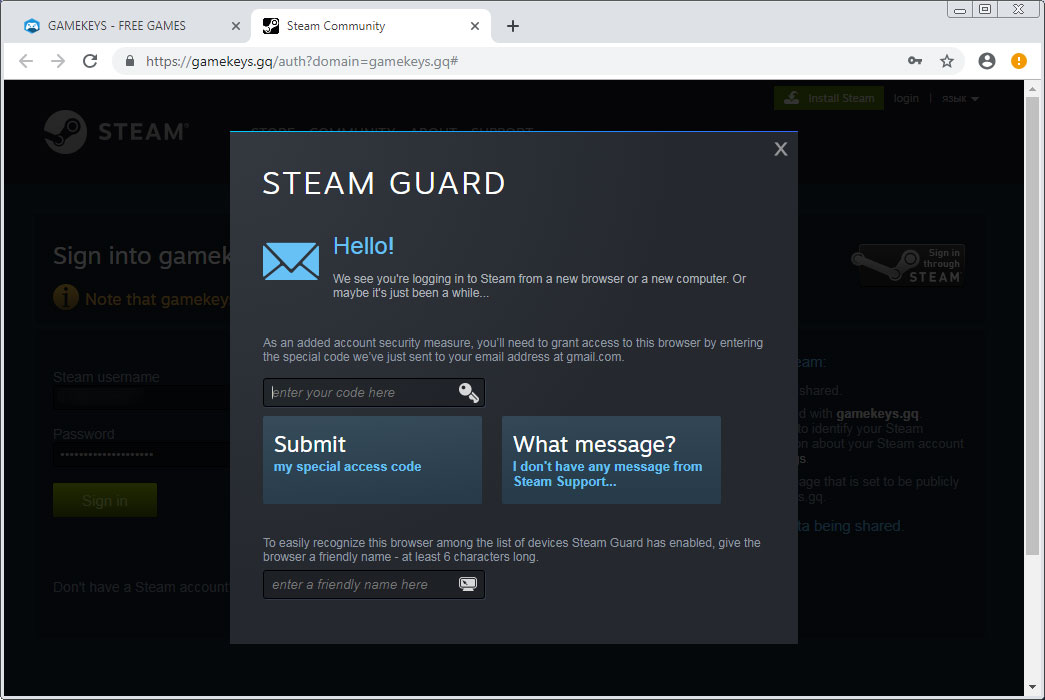
If a user falls for the scam and enters their code, the site will perform a behind-the-scenes and automated attack that logins to their account, changes the password, changes the associated email address, and changes the associated phone number. They have now essentially stolen your account.
The attackers will now use the stolen account to further spread their scam to the victim's friends list and to potentially steal the items in the victim's Steam inventory.
This leads to a repeated cycle of promotion through hacked accounts for the attackers.
Testing the scam
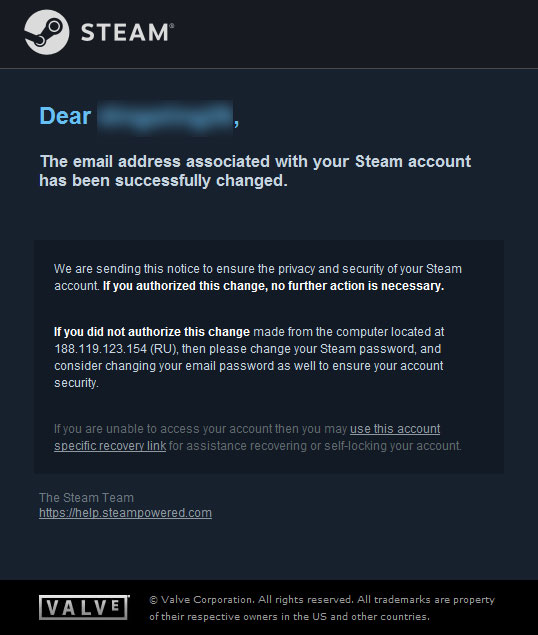
BleepingComputer tested this scam site with a Steam account and after entering our credentials, the site logged in and changed my account's email.
When an account has their email address changed, Steam will send a notification to the original email address that includes the country and address of the person who made the change. As you can see below, the IP address was 188.119.12.154 and is located in Russia, which is not my computer's IP address or country.
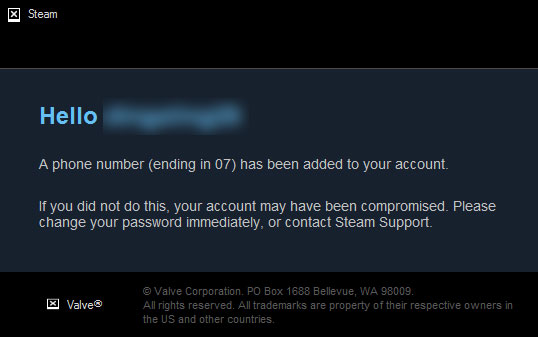
In addition to the email address being changed, the phone number will be changed as well, which will be shown through a notification sent by Steam.
Thankfully, if your account is hacked in this manner, you can open a account recovery support ticket and Steam will help you recover the account.
Unfortunately if the attackers steal or trade away the items in your inventory, Steam's Item Restoration Policy states that they will not restore any lost items.
Steam Support will no longer restore lost items. Items often exchange hands multiple times before a restoration request and this means they cannot be restored without duplicating them or removing them from another innocent user’s inventory. Duplicating items has a negative impact on everyone who trades or uses the Market by lowering the value of items.
Protecting yourself from Steam scams
Attackers are becoming more crafty and designing attacks that make it difficult to tell if you are entering your credentials into Steam or the scam site.
Knowing this, the general rule is when logging into a site via Steam, you must only do so if you are on the https://steamcommunity.com web page as shown below.
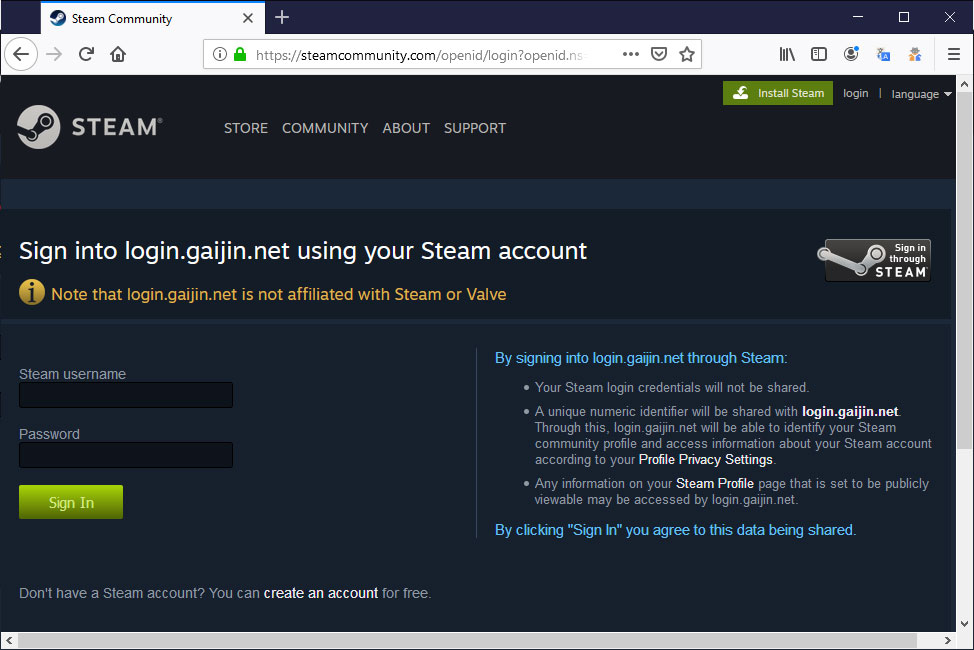
If you are any other page, or it does not show an address like this scam did in their popup, then you should never enter your credentials.
Furthermore, Steam suggests that all accounts configure 2-factor authentication through the Steam Guard Mobile Authenticator app to further secure their account. Unfortunately, in this particular scam, the attackers would still be able to bypass the 2FA as they ask you for your Steam Guard code and will be able to login if it is provided.
Thx to Quoc for the tip!


Comments
Allen - 4 years ago
Is this an automated attack or are the scammers manually changing the email and phone number and password?
Lawrence Abrams - 4 years ago
Automated. Just added that to the article to make it more clear. Thx
Allen - 4 years ago
huh, that's actually interesting, do you think the automation could be stopped if steam introduced a captcha for doing tasks like changing your email, password and phone number?
I realize there are ways to bypass it, but it could slow down the scammers for a bit if steam were to do this.
Lawrence Abrams - 4 years ago
My guess is they are utilizing SSO behind the scenes. Not familiar enough with their API to comment further.
fromFirefoxToVivaldi - 4 years ago
And instead of teaching people to look for Extended Validation certificates, which Steam, PayPal and other important services use, Firefox will be hiding EVs from the address bar. That browser is making things easier for scammers and putting the users at risk for no benefit.
Viper_Security - 4 years ago
I may also be switching browsers. love the name btw, vivaldi is an amazing browser imo.
TsVk! - 4 years ago
Along with Chrome and Safari doing the same thing. EV certificates give a false sense of security as they do not validate the company or the site only the encryption. Read more here so you understand better
https://www.bleepingcomputer.com/news/software/chrome-and-firefox-changes-spark-the-end-of-ev-certificates/
https://www.bleepingcomputer.com/news/security/extended-validation-ev-certificates-abused-to-create-insanely-believable-phishing-sites/
As Vivaldi is based on Chromium it will also be hiding the certificate display in the very near future, if it isn't doing so already.
fromFirefoxToVivaldi - 4 years ago
That may be the case in the US, but most European countries do not allow two companies the share the same name. The EV windows displays the country code, so people would know if it was registered in another country. On top of that, even in US this would require the phisher to set up a company to phish with, which means he'd be much easier to track and jail.
You're proposing to undermine the security of online banking in Europe because the US has some poorly designed laws and would allow a small windows of time between the phinishing starts and the website is shut down. Looks like the not understanding bit of your comment applies to you more than anyone else.
As for Vivaldi, they already support so many more features and customization options than any other chromium browser, that I expect them to either keep the EV certificate display, or give the user an option to enable it.
TsVk! - 4 years ago
I'm not proposing anything, I'm just some dude on the internet. I was just letting you know it's not just Firefox but all browsers who have done this, and the reasoning.
https://www.troyhunt.com/extended-validation-certificates-are-really-really-dead/
fromFirefoxToVivaldi - 4 years ago
And that reasoning doesn't apply outside US. There's nothing new in the article you've linked. Troy Hunt is a great researcher, but sadly has a purely American scope.
TsVk! - 4 years ago
People are generally just as stupid/naive when it comes to online security in Europe as they are here in Australia and also in the US. The smart ones look at the URL, a shocking majority click away blindly with or without an EV cert. That was what comprehensive testing showed.
So now EV's are history. ¯\_(ツ)_/¯.
DropZz - 4 years ago
This whole thing could be prevented if Steam would require verification when changing a E-Mail address.
Codemaster99 - 4 years ago
Interesting that it still shows the correct URL for Steam making it look authentic. Clever use what I would consider a web-browser flaw. However, common sense still prevails here. I would still default to Steam's best practice to NEVER enter your Steam information to an untrusted source.
1. Random message for a free game from a URL steamsafe.fun/?ref=freegame URL?
2. Asking me to enter in my steam creds shady website named gamekeys.gq?
To me, this should be a no brainer. Pretty obvious red flags should be indication enough.
SethNW - 4 years ago
Am I only one questioning just why Steam allows e-mail change without confirming it on old e-mail? Because that is plain stupid from security perspective. Yes, it reduces amount of tickets from people who lost their e-mail account. But it really is big security risk. Or at least thru could Alternatively include reversal link into that notification. Or they could st least request confirmation via phone, if you have authenticator on phone available. I really find this scam only working for dumb reasons to cut on work. Plus mail and other changes should require another authentication from app on phone. Blizzard really has made authenticator very simple and straight forward, and you just get notification asking to approve login or deny it. Not even code is required. But Steam really did open huge security hole in how you can change everything and Steam Guard asks no questions. Changing e-mail should not be convenient. You don't do it every day. You don't even do it once per month. Sorry for rant, but I really don't like it when companies don't take security seriously, just to cut on work. And it is not like Steam doesn't get a lot of money from me on all purchases I made.
deaththekid922 - 4 years ago
i think the problem is that alot of people forget their email adress and rather than having to deal with helping people get back into that , they allow you to change the attached email more easily , i still have an old minecraft acc tied to a deleted email adress , honestly , if more people simply understood 1 thing , none of this would happen , NOTHING IS FREE
you get a free game if you use our client -> you need to give away data the company making the client can use
you can play a game for free but.... -> alot of users will end up spending money on it , and generally f2p games arent expensive to keep running
you can try a software for free but please insert your credit card info -> no , if it was a free trial you wouldnt need to insert anything , it would just stop working after the trial is over
not even the games i gift to friends are free , i have my reasons for gifting , which is a bit weird , i really like lets plays and especially like it when someone plays a game i already know blind , because im like "oh , what will his reaction be when the boss suddenly stands back up again"
there just is no scenario where someone truly gives something away for free without any reason behind it , and thats what people dont get , if steam has prepaid cards ,and also accepts adding money via paypal , credit card , paysafecard , or prepaid cards , why would "free money hacks " exist ? they dont , but someone poor and uneducated will google "how to get game X for free" and sooner or later end up either with a virus , or with their account stolen , theres nothing steam can do , except restrict stuff so much , it becomes annoying for normal users
SethNW - 4 years ago
Sorry for double post. Can't find delete option...
Professor_Heavy - 4 years ago
Hello there. I'm a common Steam user who created an account just to comment here.
I'd like to start off by saying that these scams are by no means "elaborate". Irrelevant, I know, but I've seen these kinds of scams many times before. They're simple phishing scams. In fact, this kind of thing happens a lot. Scams often target users depending on how valuable their account is (in-game items, games, etc). I even noticed this scam myself. The site faked Steam's login page, creating a fake "window" inside the frame as if to make it look like a new window was created.
Steam's security is very easy to bypass thanks to human error of its users. Valve, the founders of Steam, really only have 2FA as the obstacle. Once scammers get through that by phishing, they have full access to the account.
Steam makes no attempt to warn you of suspicious logins. When I was still using email authentication and when someone logged into my account, they gave me an option to check the IP and locations of that particular login, and even gave me an option to lock my account. However, as you probably know, with 2FA mobile auth, they just give you a push notification with the login code. There isn't even a page to see activity history...
These scams are very common. And the consequences are massive. I'm with SethNW on this one, though. They do have some security measures, such as "trade holds", which prevent game items from being traded if 2FA was recently changed(?) or removed. But there's nothing stopping people from getting into the account in the first place. No lockdown, no suspicious activity warnings, nothing.
evil4you - 4 years ago
steam is a platform for gaming, you might visit an internet cafe or a friends house and want to login to it from there... they built the system with this in mind...
Professor_Heavy - 4 years ago
I'm aware of the reasons behind it. But that does not justify these kinds of happenings. Valve do not account for human error when it comes to scams on their service.
human123 - 3 years ago
On top of that, nearly all of them use CloudFlare to hide their operations and if you contact CF to report abuse at: https://www.cloudflare.com/abuse/form , they may comply with your first few reports but will then outright refuse to take actions and reply with empty responses! That was my personal experience.
What you can do before reporting to CloudFlare is to report through a few sites below to warn others of such phishing sites:
1.
https://safebrowsing.google.com/safebrowsing/report_phish/?hl=en/
2.
https://www.microsoft.com/en-us/wdsi/support/report-unsafe-site/
3.
https://phishing.eset.com/report/enu/
4.
https://www.phishtank.com/add_web_phish.php/
5.
https://www.virustotal.com/gui/home/url/
...
If you don't like CloudFlare or their refusals to take actions on your reports, you can try reporting directly to some of the scammers' hosting providers as listed below. One of them might acknowledge hosting such sites.
Warning: This is not an exhaustive list and there's no guarantee they will take your reports seriously either.
Hosting Provider: Garant-Park-Internet
Abuse Contact: info@invs.ru
Hosting Provider: DDOS-GUARD CORP., BZ
Abuse Contact: abuse@lacnic.net
Hosting Provider: MCHOST-NET
Abuse Contact: abuse@mchost.ru
Hosting Provider: ITLDC1-SOF1
Abuse Contact: abuse@itldc.com
Hosting Provider: SC-INTERNET-IT-20170712
Abuse Contact: support-link.ac@yandex.com
Hosting Provider: vpsville
Abuse Contact: admin@vpsville.ru
Hosting Provider: MSK_HOST-NET
Abuse Contact: abuse@msk.host
Hosting Provider: AMAZON-GRU
Abuse Contact: abuse@amazonaws.com